Subscribe To Our Newsletter
Join our 50,000+ happy customers
[mc4wp_form id=""]
We’ll Design 🎨 Your Card For Free!
Free Next Day 📦 Delivery in UK
We Ship Worldwide 🌎 ✈️

NFC business cards are transforming networking, one tap and your entire profile is instantly shared. But behind the convenience lies real risk, which brings up the critical question: Are NFC business cards safe? A compromised tag can redirect to a phishing site, a cloned card can be used to impersonate you, and hidden tracking logs can quietly map your movements. In other words, a single tap can expose far more than you think.
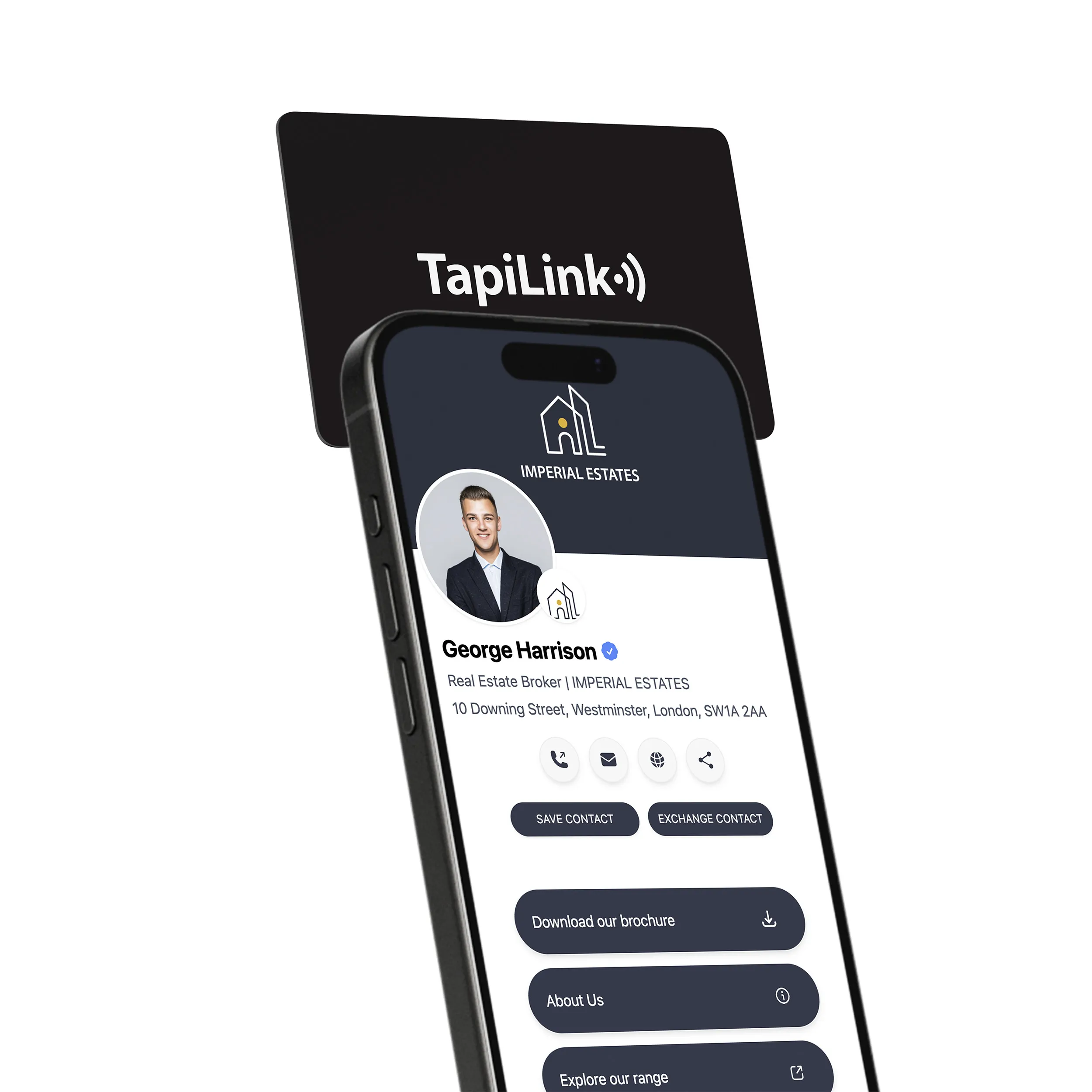
That’s where TapiLink stands apart. We deliver fully customizable NFC cards with secure profile links, remote deactivation, instant updates, CRM integration, free design, and next-day UK delivery. One card, endless connections, without compromising your security.
NFC business cards broadcast data without authentication. Any NFC-enabled device within 4 centimeters can read your card instantly. The chip requires no password or permission to transmit stored information.
An attacker places their phone near your wallet or pocket. Your contact details transfer in milliseconds without notification. The stolen data includes your name, phone number, email, and company information. Attackers use this verified information for spear-phishing campaigns. In 2023, security researchers collected data from 47 conference attendees using hidden readers
Relay attacks use two coordinated devices to steal your card data remotely. A Skimmer device placed near your card intercepts the NFC signal when you tap it. This device immediately transmits the captured data through WiFi or cellular networks to a second device called a Relayer.
The Relayer can be located hundreds of feet away or even in another country. It replays your card’s exact signal to a legitimate NFC reader, fooling it into believing your physical card is present. Attackers complete transactions or trigger secure actions without ever being near you.
An NFC tap can deliver a phishing page or malware in seconds. A malicious tag can redirect your phone to a convincing fake login (corporate VPN, CRM, or email) so you type credentials that go straight to the attacker. On Android, historically tracked vulnerabilities (e.g., NFC/intent handling bugs) have let tags trigger background app downloads or launch intents that accelerate compromise.
Once malware is installed, attackers can intercept SMS one-time passwords, exfiltrate contacts and files, capture corporate tokens, and install remote-access tools that pivot into corporate networks.
Most NFC business cards don’t hold the full profile on the chip itself. They store a short URL or unique ID that points to an online profile. Each tap creates a log entry with time, date, and device details, and in many cases, approximate location through IP data.
Over time, this generates a behavioral map of where and how often the card is used. At large events, such data can reveal a person’s movement between booths or sessions, creating a silent record of surveillance without the user’s explicit awareness.
One of the most overlooked risks of NFC business cards is how little control users have over the data being collected. Every tap can log time, location, device type, and even browsing behavior on linked profiles, yet most recipients are unaware this tracking is happening.
Card owners and providers often use these analytics, but recipients rarely get clear disclosure. Data collection is usually hidden in terms of service, and most platforms don’t provide expiry or deactivation features. This leads to continuous data gathering without proper consent.
Your NFC business card broadcasts data constantly without requiring any authentication. Anyone with a smartphone can read it from your pocket or bag. The chip transmits information unencrypted in simple formats attackers intercept easily.
Standard cards lack the tokenization and dynamic codes protecting your credit card payments. The chip contains a permanent unique identifier enabling unauthorized tracking of your movements across events and locations.
When you lose your card, it stays active until you manually deactivate it. No remote wipe exists. Unlocked tags let attackers reprogram the destination link to redirect victims elsewhere.
NFC cards transmit data via radio waves at 13.56 MHz frequency. Attackers use concealed equipment with modified antennas to passively intercept this wireless communication without your knowledge.
They capture the unencrypted URL linking to your digital profile or vCard data containing your contact information. This URL often includes a unique persistent identifier tracking your card. While NFC operates within 4 centimeters, specialized equipment extends interception range beyond one meter
Attackers use concealed NFC readers, modified smartphones or dedicated devices hidden in bags, pockets, or clothing to steal your card data without permission. They position the skimmer within 4 to 10 centimeters of your card in crowded networking events, elevators, or public transit.
The attacker captures your complete vCard containing your name, company, title, phone, email, and social links. Stolen identifiers enable tracking your digital platform activity, building detailed profiles for sophisticated phishing campaigns.
Attackers embed premium-rate phone numbers or SMS shortcuts into NFC cards. When you tap the card, your phone automatically initiates calls or sends messages to high-cost numbers without warnings.
Each interaction generates charges from £5 to £50 on your bill. Malicious cards redirect to websites running silent cryptocurrency miners, draining your battery and data plan while generating unauthorized costs you discover weeks later.
NFC business cards offer speed and convenience, but they also expose you to serious security risks. The following practices protect your data, limit unauthorized access, and keep your professional information secure.
Turn off NFC in your phone’s settings when you’re not actively using it. This prevents accidental taps and blocks unauthorized scanning attempts in crowded spaces. Attackers can’t read your card if the technology sits dormant. Enable NFC only when you need to share or receive contact information, then disable it immediately afterward.
Confirm the legitimacy of any person or device requesting a tap. Look for official event badges, company credentials, or verified staff identification.
Avoid tapping cards at unmarked kiosks or suspicious terminals. Ask questions if something feels wrong. Legitimate professionals won’t pressure you into immediate card exchanges.
Select NFC card providers with ISO27001:2022 and GDPR certifications. These compliance standards guarantee encrypted data transmission and secure server infrastructure. Review provider security whitepapers before purchasing.
Check for features like remote card deactivation, access logs, and regular security audits. Avoid cheap providers lacking transparent security documentation.
Review all permissions requested by NFC business card apps before installation. Grant only essential access like NFC and network connectivity.
Deny requests for location tracking, contact lists, or camera access unless absolutely necessary for core functionality. Revoke unnecessary permissions in your phone’s settings after installation. Delete apps requesting excessive access.
Apply payment card security practices to business cards. Use devices with biometric authentication like fingerprint or face recognition.
Set transaction limits if your provider offers them. Monitor your card’s activity logs regularly for unusual scanning patterns. Treat your business card with the same caution you apply to credit cards.
Contact your card provider immediately if you notice unauthorized scans, unexpected profile changes, or suspicious access patterns in your analytics dashboard. Report lost or stolen cards within minutes to trigger remote deactivation.
Document any phishing attempts or malicious redirects linked to your card. Fast reporting limits damage and helps providers patch vulnerabilities.
Keep your contact information current to maintain control over what recipients see. Outdated details create confusion and reduce your credibility. Regular updates also force you to review your profile’s security settings.
Check for unauthorized changes during each update session. Remove old links or information you no longer want shared publicly.
If your NFC card integrates payment functions, demand PCI DSS compliance from your provider. This standard mandates end-to-end encryption for all financial transactions.
Verify that payment data is never stored directly on the card chip. Confirm the provider uses tokenization to replace actual card numbers with secure tokens during transmission.
NFC security advances through AI-powered threat detection, biometric authentication requirements, and blockchain-based verification systems. Tokenization will replace static identifiers with dynamic codes that change per transaction. Quantum-resistant encryption protects against next-generation computing threats.
Dedicated security chips will isolate NFC data from device operating systems. Real-time threat intelligence networks share attack signatures globally, creating collective defense systems that learn and adapt from every attempted breach across all platforms.
NFC business cards are a powerful step forward in modern networking, fast, eco-friendly, and endlessly flexible. Yet it’s important to acknowledge the security risks, from phishing and cloning to hidden tracking, and choose a provider that prioritizes protection as much as convenience.
With TapiLink, you get both secure digital profiles, instant updates, CRM integration, and free custom design, all with worldwide shipping and next-day delivery in the UK. Ready to upgrade your networking game? Tap smarter with TapiLink today.
Answer: Yes. If your NFC card is linked to a secure online profile, you can disable or revoke access remotely. This ensures your details aren’t misused even if someone finds the physical card.
Answer: Most modern iPhones and Android devices support NFC scanning. For older phones without NFC, a QR code or direct profile link offers a reliable fallback.
Answer: No. The chip usually contains only a URL or unique identifier. Your complete profile and sensitive information remain stored securely online, not on the card itself.
Answer: Yes. The tap action activates the link, but the recipient’s device must have internet access to load and view your digital profile.
Answer: Absolutely. One reusable NFC card can replace hundreds of printed paper cards, helping reduce waste and supporting sustainable networking practices.
Join our 50,000+ happy customers
Copyright © 2025 TapiLink, made with ❤️ in United Kingdom. TapiLink is a trading name of SERVICEWORLD LIMITED (company number: 13239157), whose registered office is at 34 Green Street, London, England, E7 8BZ
Subscribe to our newsletter below and get 10% exclusive discount on your first order.