Subscribe To Our Newsletter
Join our 50,000+ happy customers
[mc4wp_form id=""]
We’ll Design 🎨 Your Card For Free!
Free Next Day 📦 Delivery in UK
We Ship Worldwide 🌎 ✈️

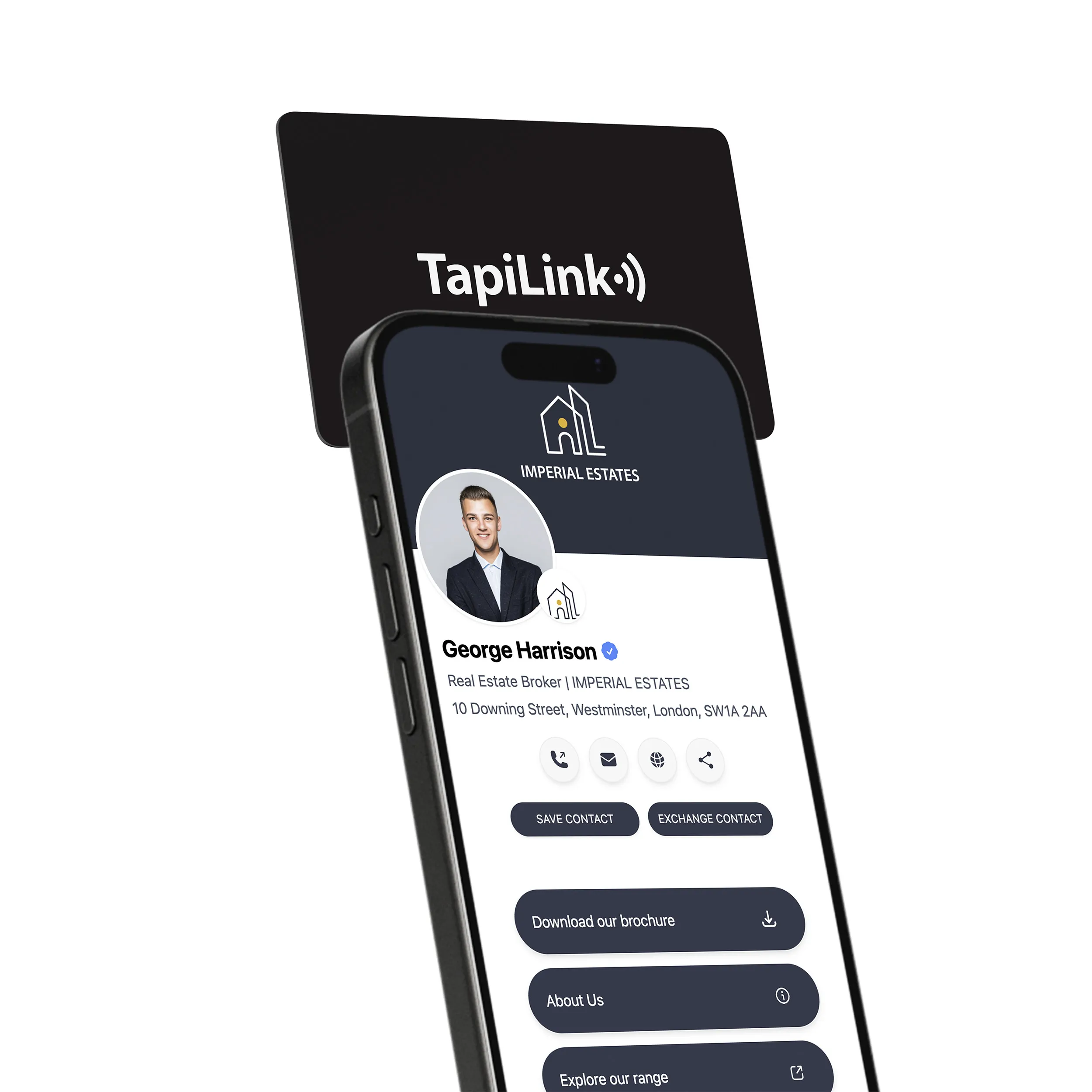
Imagine standing in a crowded industry expo. You take out a sleek NFC business card, hold it near a prospect’s phone, and within a second your full digital profile appears. This tap-to-share moment feels effortless, and it is powered by the same near-field communication technology used in Apple Pay, Google Wallet, and thousands of modern access-control systems. According to Stripe, “NFC payments are generally considered secure,” but the technology is still exposed to risks such as eavesdropping, data modification, relay attacks, and unauthorized reading. Convenience does not remove the need for strong security.
Security and privacy must therefore be a priority when replacing traditional paper business cards with digital NFC cards. Recent industry reviews and NFC Forum guidance highlight that many low-cost NFC tags contain persistent, hard-coded URLs. These static links can be discovered over time through brute-force scanning, automated crawlers, or simple sharing. Once exposed, private contact information such as email addresses or phone numbers can become publicly accessible without the owner’s knowledge. A 2024 digital-card audit found that 27 percent of NFC business cards still used unprotected static URLs, creating long-term privacy vulnerabilities.
For small business owners who operate under GDPR, CCPA, or other data protection frameworks, these risks are not just technical issues. They directly affect brand reputation, customer trust, and compliance responsibilities. Understanding how NFC cards store, transmit, and protect data is the first step in choosing a secure and reliable NFC business card platform that supports encryption, authentication, dynamic URLs, and complete lifecycle control.
Near-field communication (NFC) business cards embed a tiny NFC chip inside a plastic nfc card, metal card or other eco-friendly material. When a recipient brings an nfc device such as a smartphone within a few centimetres of the card, the chip transmits a URL that opens your digital profile – no app, no camera and no fumbling with traditional paper cards. For small business owners who juggle networking, marketing and sustainability goals, this simple tap experience feels almost magical and saves time that’s better spent building relationships.
Before deciding which format best fits your brand, consider how NFC stacks up against familiar alternatives:
• NFC: Share a full digital profile in under a second with an nfc tap.
• QR codes: Fast but require camera activation and screen alignment.
• Traditional paper cards: Immediate handoff but no digital follow-up baked in.
Security privacy
• NFC: Supports encryption, authentication and remote deactivation.
• QR codes: Visible patterns can be photographed, reproduced or tampered with.
• Paper cards: No security; anyone can copy or lose the information.
Sustainability
• NFC: Reusable cards slash paper waste and printing costs.
• QR codes: Still printed on paper signage or cards that may be discarded.
• Paper cards: Require constant reprints when contact details change.
With adoption accelerating across industries – from boutique consultancies to bustling cafés – the question shifts from “Should I try an NFC card?” to “How do I secure it?” Understanding the underlying tech is the first step toward managing those security implications effectively.
NFC works by creating a low-power radio link between two endpoints that are typically four centimetres apart or less. When the tag in your card and the reader in a phone connect, they exchange data packets and close the session in milliseconds, minimising the window for interception. Guidance on interception of communications notes that good encryption further reduces the already small risk of eavesdropping or data modification during this handshake.
For small businesses, the practical applications keep expanding:
• Networking events: Sales reps tap share their contact details, LinkedIn profiles and brochures without carrying boxes of paper business cards.
• Retail point of sale: Loyalty program enrollment happens instantly when customers tap an nfc tag at checkout.
• Hospitality: Hotel staff offer digital concierge services by tapping guest phones, providing Wi-Fi credentials, menus or local recommendations.
• Field service: Technicians leave a secure nfc card on-site so clients can request support or view maintenance logs with one tap.
• Pop-up shops: Vendors update pricing or promotions on the fly because the digital profile behind each card platform is editable in real time.
Swapping data with a simple tap feels effortless, yet that same ease can introduce vulnerabilities if you don’t pay attention to security privacy fundamentals.
According to Tapilink’s analysis of six hidden security risks of NFC business cards, small firms must watch for everything from unauthorized access to logistical headaches when managing dozens of cards across a team. In practical terms, here’s what that looks like:
• Unauthorized access: Anyone close enough with the right reader might skim data from exposed nfc tags.
• Insufficient encryption: Limited processing power on low-cost plastic nfc cards can leave data in plain text.
• Data tampering: Malicious actors can overwrite the URL embedded in an nfc chip and redirect recipients to phishing sites.
• Device exploitation: Compromised cards can trigger scripts that probe phone vulnerabilities.
• Lost stolen cards: A misplaced secure nfc business asset becomes an immediate risk if it can’t be remotely deactivated.
• Centralised management gaps: Tracking issuance, revocation and updates for a growing workforce quickly turns into an IT burden.
While these threats span both the physical card and the underlying network, one unifying factor is that attackers need proximity or a way to hijack the data path.
Stripe notes that “NFC payments are generally considered secure” yet still cautions against risks such as eavesdropping and data modification, illustrating that even well-hardened payment networks face similar challenges to business card exchanges. That context matters because small businesses often assume the same level of protection automatically applies to every nfc card they hand out.
• At a major trade fair, researchers demonstrated how unprotected vCard payloads could be skimmed from attendee badges, exposing names, job titles and emails in seconds.
• A marketing agency once discovered its branded nfc cards were silently updated by attackers to point to a spoofed login page, harvesting CRM credentials before the breach was caught.
When compared with QR codes, NFC’s short-range requirement does remove some attack vectors, yet QR images can’t be silently overwritten the way an nfc chip can. Traditional paper cards avoid digital threats entirely but add zero security if they fall into the wrong hands. Each method carries its own profile of convenience versus risk – NFC just happens to blend cutting-edge efficiency with a fresh set of security considerations.
NFC business cards don’t just share contact details; every tap can generate analytics such as timestamp, device type and location. When that information funnels into a card platform’s dashboard, it becomes personally identifiable data subject to regulations and, if mishandled, reputational fallout. Small business owners who value customer trust must therefore weigh the convenience of real-time insights against the responsibility to collect and store that data ethically.
Beyond analytics, the link inside an nfc chip often persists indefinitely. Because the tag’s URL rarely changes, hard-coded URLs can surface over time through web crawlers or brute-force discovery, potentially exposing phone numbers and email addresses without your knowledge. The longer a card circulates, the higher the chance that someone – human or bot – will stumble onto the live profile.
Privacy protection ultimately comes down to control. Users need clear choices about what information the card reveals, the ability to revoke or update that data instantly and transparent consent prompts for anyone submitting their details in return. Without those mechanisms, even the strongest encryption can’t prevent misuse once personal data lands in the wrong CRM or marketing list.
Hard-coded links present a particular challenge because you rarely know who might have saved or shared the URL. Left unchecked, they create a backdoor into your professional identity long after you’ve changed jobs or phone numbers.
Steps to limit that exposure include:
• Choose card providers that support dynamic URL rotation or remote deactivation.
• Schedule periodic audits to refresh or retire outdated profiles.
• Minimise sensitive details; share essentials only, like work email rather than personal numbers.
• Host profiles on HTTPS-secured pages and enable two-factor authentication for edits.
• Monitor access logs to spot unusual traffic patterns that could hint at scraping.
By pairing technical safeguards with proactive management, you can enjoy the fast, eco-friendly benefits of NFC business cards while keeping control of your data footprint.
Scrambling data in transit is the first and most important line of defense. A technical article on NFC security notes that symmetric and asymmetric algorithms such as AES-128, AES-256, RSA and ECC underpin secure contactless communication. Symmetric keys keep transactions lightning-fast for routine exchanges, while public-key systems add a heavier – but highly robust – layer for scenarios that demand maximum confidentiality, like payments or sensitive client data transfers.
Encryption is only half the story. Authentication protocols verify that the device reading your card is genuine and that you’re the rightful cardholder. Mutual authentication lets both endpoints confirm each other’s identity before sharing data, thwarting spoofed readers. Challenge-response systems add a dynamic handshake so replay attacks fall flat, and two-factor authentication combines something you have (the nfc card) with something you know (a PIN) or something you are (biometrics) for an extra barrier. Stripe’s own payment-security guidance shows this layered approach is what turns quick taps into confidently trusted exchanges.
Solid cryptography also relies on airtight data integrity. Ensuring that no one alters the packets en route protects brand credibility just as much as customer privacy.
When you’re ready to harden your card platform, put these safeguards at the top of your checklist:
• Hash functions (such as SHA-256) generate a digital fingerprint for each data packet so even a single-bit change signals tampering.
• Message authentication codes (MACs) attach a short validation string that only devices with the shared secret key can compute, stopping data modification in its tracks.
• Digital signatures leverage asymmetric keys to prove the sender’s identity and verify that the content hasn’t been altered since it left your card platform.
• Schedule regular firmware and app updates to close newly discovered vulnerabilities before attackers attempt to exploit them.
• Run quarterly security audits – penetration testing, code reviews and access-log analysis – to validate that encryption, authentication and integrity controls are still fit for purpose.
Combined, these measures create a multilayered barrier that shifts NFC business cards from “nice-to-have tech” to a secure digital asset you can confidently hand out at any networking event.
Small business owners in the UK and abroad must meet a patchwork of privacy laws any time they collect personal data – even with something as seemingly simple as an NFC tap. The General Data Protection Regulation (GDPR) demands lawful bases for processing and clear disclosure, while frameworks like CCPA in California and HIPAA in healthcare add extra layers if you operate internationally or handle sensitive information. Failure to comply can mean steep fines, damaged brand reputation and lost customer trust.
As Tapilink observes, “Regulations like GDPR, CCPA, and HIPAA have made it clear: transparency, consent, and responsible data collection and management are mandatory.” Putting those words into practice starts long before your next trade-show badge is printed.
The most reliable route is a consent-first mindset. That means prompting contacts to agree before their details flow into your CRM, limiting data capture to what you genuinely need and storing it on encrypted, access-controlled servers. It also means documenting retention periods so old contact records don’t linger indefinitely and offering a one-click way for individuals to request deletion.
Once you fold these principles into your networking workflow, compliance transforms from a box-ticking exercise into a differentiator – showcasing your commitment to privacy at every interaction.
Follow this step-by-step plan to weave legal safeguards into everyday card sharing:
• Map your data flows: Identify where personal data enters, how it’s stored, who can access it and when it’s deleted.
• Craft a clear consent statement: Display it before tap share or on the profile page so recipients understand why you’re collecting their details.
• Enable opt-in fields: Let leads decide whether to receive newsletters or product updates instead of assuming permission.
• Encrypt storage and transport: Use HTTPS, AES-256 databases and role-based access controls on your card platform.
• Automate retention rules: Purge stale contact records after a set period unless renewed consent is obtained.
• Maintain audit logs: Track who accessed or modified data to demonstrate accountability during inspections.
• Lower legal risk and potential fines
• Enhanced brand reputation for respecting privacy
• Stronger customer trust, translating into longer-term relationships
By embedding these measures now, you’ll pave the way for a smoother rollout of any future privacy regulations – and set the stage for secure, compliant growth with solutions like ours at TapiLink.
Here at TapiLink, we built our platform from the ground up with security privacy at its core, so you can enjoy lightning-fast networking without worrying about data leaks or compliance gaps. Every digital profile is hosted on an HTTPS-encrypted card platform, and each nfc tap triggers a secure handshake that mirrors the same AES and RSA protections outlined by RFID industry experts earlier in this guide. Because our platform is cloud-based, you can update job titles or phone numbers instantly – no reprints, no stale information floating around the web.
What really sets us apart is the combination of enterprise-grade safeguards and small-business flexibility:
• Dynamic URLs: Each card can generate a fresh link on demand, blocking the hard-coded exposure risk that plagues many nfc cards.
• Remote deactivation: Lose a card? Toggle it off from your dashboard so the nfc chip becomes inert.
• Customizable encryption levels: Choose default AES-128 for speed or step up to AES-256 and ECC for highly sensitive roles.
• Two-factor profile edits: Pair biometrics or a one-time PIN with every change to stop unauthorized updates.
• Unlimited updates and transparent change logs: Keep auditors happy and contacts current without printing another plastic nfc card.
• Apple Wallet integration: Store your secure nfc business credentials on iOS without sacrificing encryption or user control.
By delivering these features with no monthly fees, we make high-end security accessible to independent consultants, boutique retailers and hospitality teams alike.
• A freelance designer cut paper waste by 90% and still met GDPR obligations thanks to dynamic consent prompts built into each tap share.
• A family-run café replaced paper loyalty cards with branded nfc tags, then remotely disabled a lost batch within minutes – eliminating fraud and protecting customer data.
• A regional property firm rolled out 50 metal cards to its agents, leveraged CRM export for instant lead capture and saw a 20% increase in follow-up calls while maintaining full compliance.
• Our mission is simple: put sustainable, user-centric networking tools in your pocket without compromising security. We innovate so you can focus on growing your business, confident that every connection is protected by best-in-class technology.
Paper business cards are easy to lose, QR codes are easy to copy and unchecked NFC tags can quietly expose personal details. By prioritising encryption, authentication and consent-first data handling, you transform a simple tap into a secure digital handshake – protecting your reputation and your customers alike.
Our secure nfc business solutions give small business owners the peace of mind that every card, tap share and profile update aligns with best-practice security privacy standards and global regulations such as GDPR.
Learn more about TapiLink’s secure NFC business card solutions or contact us for a demo.
Join our 50,000+ happy customers
Copyright © 2025 TapiLink, made with ❤️ in United Kingdom. TapiLink is a trading name of SERVICEWORLD LIMITED (company number: 13239157), whose registered office is at 34 Green Street, London, England, E7 8BZ
Subscribe to our newsletter below and get 10% exclusive discount on your first order.